API Security Is A Growing Concern
As the world around us becomes more and more connected via internet connections, the need to build secure networks grows infinitely. APIs continue to be an integral business strategy across industries, and it doesn’t appear to be slowing down anytime soon, especially with the rise of IoT.
The number of public APIs listed on apihound hovers around 50,000, while the number of private APIs is assumed to be more than the number of public APIs.
That’s a lot of data being passed over the web, some if it being incredibly sensitive.
It seems like at least once a week we hear about another company getting hacked, and having thousands of user’s information exposed. Consumer’s patience with lax security is wearing thin.
So why is it that API security is still not widely practiced? How can you make sure not to get on a consumer’s list of companies they hope to never use again?
Simple: stay ahead of your opponent.
Always Assume Everyone Wants Your Data
All APIs are not created equal, and not all vulnerabilities will be preventable. An API that is gathering weather information does not need to take the same precautions as an API that is sending patient’s medical data.
However, a good rule of thumb is to assume that everyone is out to get your data. Think about it as being the doomsday prepper for your API. If you prepare for the worst-case scenario, anything else that might go wrong will be handled with ease.
Authenticate First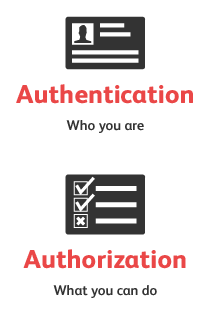
Make sure that you authenticate at the web server before any info is transferred.
Authentication and authorization are commonly used together:
Authentication is used to reliably determine the identity of an end user.
Authorization is used to determine what resources the identified user has access to.
On the web, authentication is most often implemented via a dialog that prompts for username and password. For added security, software certificates, hardware keys and external devices may be used.
Once the user is authenticated, the system decides which resources or data to allow access to.
For APIs, it is common to use some kind of access token, either obtained through an external process (e.g. when signing up for the API) or through a separate mechanism (e.g. OAuth).
The token is passed with each request to an API and is validated by the API before processing the request. Alternatively, the dialog method may be used.
The best solution is to only show your authentication key to the user once. It’s their responsibility to hold that key near and dear. You wouldn’t trust someone who kept losing the spare keys you gave them, would you?
Why Are You Still Using HTTP?
Encryption is generally used to hide information from those not authorized to view it. On the Internet, often SSL is used to encrypt HTTP messages, sent and received either by web browsers or API clients.
A limitation of SSL is that it only applies to the transport layer. Data that also needs protection in other layers require separate solutions.
Signatures are used to ensure that API requests or response have not been tampered with in transit. The message itself might be unencrypted, but must be protected against modification and arrive intact.
Encryption and Signatures are often used in conjunction; the signature could be encrypted to only allow certain parties to validate if a  signature is valid - or the encrypted data could be signed to further ensure that data is neither seen or modified by unwanted parties.
signature is valid - or the encrypted data could be signed to further ensure that data is neither seen or modified by unwanted parties.
Know Your Vulnerabilities
The area of security vulnerabilities is a diverse field. There are many different attacks with different methods and targets. One way to categorize vulnerabilities is by target area:
- Network / OS / Driver: issues in the operating system and network components (e.g. buffer overruns, flooding with sockets, DOS attacks)
- Application layer: issues in the hosting application server and related services (e.g. message parsing, session hijacking or security misconfigurations)
- API / component: functional issues in the actual API (e.g. injection attacks, sensitive data exposure, incomplete access control)
What Are Best Practices for API Security?
Treat Your API Gateway As Your Enforcer
The API gateway is the core piece of infrastructure that enforces API security. Unlike traditional firewalls, API security requires analyzing messages, tokens and parameters, all in an intelligent way.
The API gateway checks authorization, then checks parameters and the content sent by authorized users. It then ensures that when logs are written that they're redacted, that the customer data isn't in the logs, and does not get written into storage. And it accomplishes these steps in the proper order.
 When configuring throttling rules, usage of API keys or OAuth, the API gateway acts as the enforcement point.
When configuring throttling rules, usage of API keys or OAuth, the API gateway acts as the enforcement point.
This is the traffic cop, ensuring that the right users are allowed access, and the wrong ones are being blocked. An API gateway can be used either for incoming requests, coming into your APIs.
The API gateway allows you to encrypt parts of the message or redact confidential information, then meter, control, and analyze how your APIs are being used.
So much can be done with an API gateway, but its main benefit is moving security from the application to your organizational infrastructure, allowing you to treat the security of your application and API like a first-class citizen.
Use Quotas and Throttling
If you produce an API that is used by a mobile application or particularly rich web client, then you will likely understand the user behavior of those applications clients.
If a typical user calls the API once or twice per minute, it’s unlikely that you will encounter several-thousand requests per second at any given time.
A behavioral change such as this is an indication that your API is being misused.
Throttling also protects APIs from Denials of Service and from spikes. It’s possible to implement sophisticated throttling rules to redirect overflows of traffic to backup APIs to mitigate these issues.
Detect Insecure API Calls With Sniffers
Insecurity can proliferate in mobile apps – these applications often reference several APIs, and if any of these APIs are insecure, then the information obtained by the app is compromised.
One practical method to locate mobile app security issues is to run a sniffer to analyze the call-home traffic from the mobile app.
Often times you’d be surprised at the information passing back to the internet: confidential information, passwords, you name it.
How to Start Security Testing Your APIs
With ReadyAPI, it's easy to add security scans to your new or existing functional tests with just a click. It's easy to create scans, so security testing can easily be accomplished by both testers and developers on your team.
This helps ensure that critical API security testing occurs every time your tests run and is no more considered as an afterthought. Thus, making your APIs more secure and safe from the most common attacks.
ReadyAPI allows you to:
- Quickly generate security tests from your functional tests with just a click, and run them against your API
- Protect your APIs by running standard scans designed to mimic standard hacking techniques
- Create custom scans or layer them over existing scans to cater to your own use case
- Integrate API security with automation to ensure your APIs stay secure even after a code change
Looking for more great content?
Read DevOps Trends
Watch a webinar on Practical Tips to Achieve API Security Nirvana